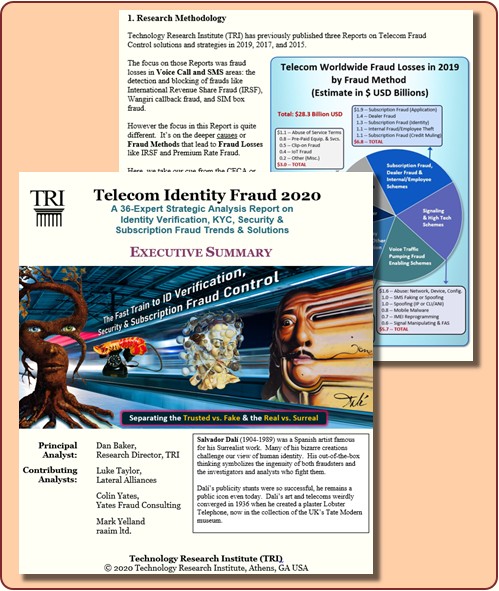
A 36-Expert Strategic Analysis Report on Identity Verification, KYC, Security & Subscription Fraud Trends & Solutions |
 |
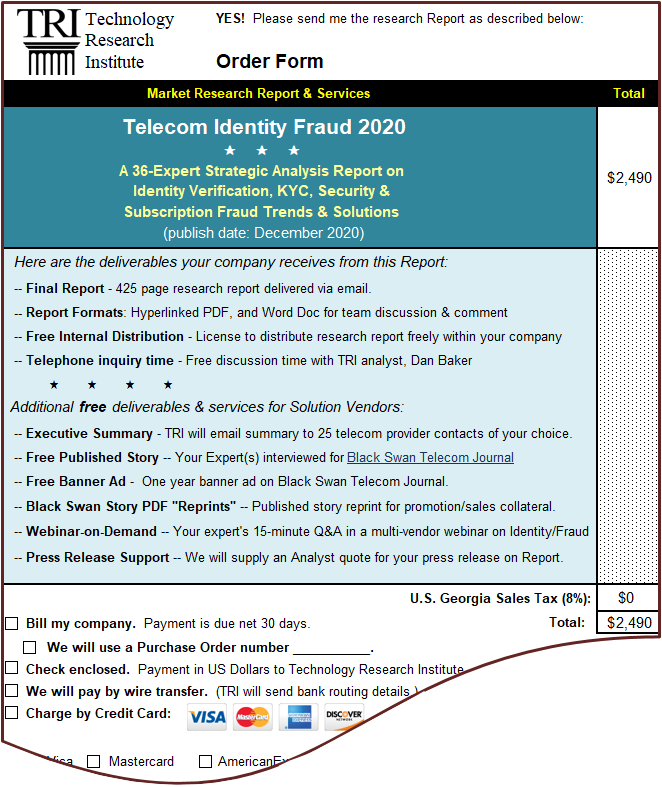
| Price: | $2,490 USD | |
|---|---|---|
| Publish Date: | December 2020 | |
| Report Length: | 425 pages | |
| Principal Analyst: | Dan Baker, TRI Research Director/Owner | |
| Contributing Analysts: | Colin Yates, Yates Consulting Ltd. Luke Taylor, Lateral Alliances Mark Yelland, raaiim |
Report Author Letter
| Dan Baker TRI Research Director/Owner & Report Author |
 |
Dear Colleague:
Getting excellent in Subscription Fraud Control. . . Identity Verification. . . and Advanced Security is crucial for telecoms. And that goal is not easy to achieve.
All these areas will require fresh systems, fresh investments, and fresh practices. Plus much broader enterprise intelligence sharing is needed to access databases and drive analytics/machine learning.
Today the financial industry is way ahead of telecoms in this identity/security sphere. And yet, the smartphones that telecoms safeguard have become the digital equivalent of ATM bank machines.
The challenges are immense! But the upgrades are mandatory: telecoms simply must enhance their mobile/consumer protections, reduce subscription theft, and enable greater volumes of their own on-line sales.
Over the past 12 months, as TRI Research Director, I explored these identity/security realms of fraud control, interviewing dozens of industry experts to produce this 425-page analyst report, Telecom Identity Fraud 2020. Why not consider buying a copy for yourself and your entire team?
Who Benefits from the Report?
The Report is written for both telecom managers of fraud/security programs and the solution vendors who provide the necessary technology, automation, and services to stay ahead of the fraudsters and criminals:
- Fraud/security experts at telecoms will better grasp the confusing technology and systems that surround identity fraud and security control. You’ll also learn who the leading vendor players are across the many domains and understand each one’s strengths.
- For a solution vendor, the Report provides key competitive intelligence. You’ll spot market opportunities where your company’s expertise can be applied. The Report will also help you answer the vital question: which corner(s) of the telecom identity fraud solution sector should I invest my next R&D and marketing dollar?
Insights from Three Dozen Expert Contributors
I call myself the “author” of this Report, but in reality, the perspectives of the 36 expert contributors I interviewed deliver 90% of the Report’s analysis and value. Putting together this Report was truly a collaborative effort.
When I interviewed the solution vendor experts, I asked them two key questions: 1) how is your company delivering value in telecom identity fraud?; and 2) what differentiates you from your rivals?
In short, the focus was on their value propositions. After recording our discussion, I lightly edited their remarks, put them into a Q&A format, and wrote an introduction. The experts then edited their stories to accurately express their company’s direction and strengths in the telecom sector.
Our research cast a wide net. We not only interviewed experts at familiar telecom fraud/security firms like Allot, Mobileum, Subex, and iconectiv. We also reached fraud-fighting pros at big cross-industry solution vendors such as SAS Institute, LexisNexis Risk Solutions, and FICO.
A Highly Accessible Report
The Report is designed for easy access and reference. The subjects are thoroughly indexed and hyperlinked inside the Chapters.
- You can distribute the PDF version to anyone on your internal team to read or even print out the Report. We will also send you the Report in MS Word format so you can insert your own notes in the text, and enable team discussions of the Report.
- Don’t be intimidated by the 425 pages in this study. I recommend reading the 67-page Strategies, Solutions and Marketing Chapter first: that’s where I summarize the perspectives of all the industry experts and draw my conclusions. From there, you can drill down for greater detail by reading each expert’s perspective in the Chapters that cover the various threats and solution types.
Scan the Details. . . Sample the Research
The best way to know if Telecom Identity Fraud 2020 is a good investment for your firm is to download the Executive Summary and read it. You’ll see the wide domain intelligence we gathered and the way we organized and wrote the Report.
Also be sure to scan the table of contents, the bios of the 36 expert contributors, and the free services that come with your Report purchase.
Sincerely,

Dan Baker
Report Author & Research Director/Owner, TRI
P.S.
As with any research you buy from TRI, your satisfaction is fully guaranteed. If the report does not deliver the quality of research you expect, within 30 days let us know and we’ll send a full refund on your purchase.
Deliverables
Research Report Deliverables
Here are the Research Report deliverables your company receives from this Report:
- Final Report — 425 page research report delivered via email.
- Report Formats — Hyperlinked PDF, and Word Documents for team discussion & comment.
- Free Internal Distribution — License to distribute research report freely within your company.
- Telephone inquiry time — Free discussion time with TRI analyst, Dan Baker.
Additional Services for Solution Vendors
Additional free deliverables & services for Solution Vendors:
- Executive Summary — TRI will email summary to 25 telecom provider contacts of your choice.
- Free Published Story — Your Expert(s) interviewed for Black Swan Telecom Journal.
- Free Banner Ad - One year banner ad on Black Swan Telecom Journal.
- Black Swan Story PDF "Reprints" -- Published story reprint for promotion/sales collateral.
- Webinar-on-Demand -- Your expert’s 15-minute Q&A in a multi-vendor webinar on Identity/Fraud
- Press Release Support -- We will supply an Analyst quote for your press release on Report.
Executive Summary
We are pleased to offer a FREE copy of the Executive Summary. While its 21 pages contain less than 5% of the Report's content, it shows you the wide breadth of research and gives you a flavor for the intelligence inside the full Report. Also, please see the Order Form to learn about valuable free services that come with the Report's purchase of $2,490 U.S. Dollars. <>/p> To download the 21-page Executive Summary in PDF click below link: 
|
Order Form
Download the Excel order form for the research report here |
Satisfaction Guarantee
Here's our guarantee. Within 30 days of receiving any research Report you buy from TRI, if you're not delighted with its quality, you may notify TRI that you wish to return it. We will mail out a complete and prompt refund upon the return of the research.
Table of Contents | |
| 1. Executive Summary (21 pages) | |
| a. | Research Objectives & Methodology |
| b. | Mobile Threats: Theft, SIM Swap & Account Takeover |
| c. | Network, Behavioral & KYC Identity Verification |
| d. | Subscription Fraud & the Hub of Identity Decisions |
| e. | Insider/Partner Fraud & Data Access Issues |
| f. | High Tech Threats in Signaling & Mobile Malware |
| g. | IoT & 5G Security and Connectivity |
| h. | Mobile Money & Telecoms Monetizing Identity |
| i. | Number Databases, Wangiri and the PBX Threat |
| j. | Real-time Enterprise & Inter-Carrier Handshakes |
2. Mobile Threats in Device Theft, SIM Swapping & Account Takeover (34 pages)
 | |
| a. | Verizon Gives Details on its 2018 Mobile Handset Losses and its ID Verification & Subscription Fraud Programs |
| – An Inside Look at Verizon's ID Verification & Anti-Fraud Programs | |
| – Verizon's Practice of Unlocking 4G LTE Handsets at Time of Purchase | |
| – Other U.S. Carriers Unlock Phones Only After Phones are Paid for in Full | |
| – The Fraud Types Verizon Experiences: Identity, 1st Party & Synthetic | |
| – Verizon's Growing 4G Handset Theft Problem | |
| – Why Handset Theft is Increasing at Verizon | |
| – Why Verizon is a Bigger Target for Device Theft than Competitors | |
| – Observations on Combating Fraud and Device Theft | |
| – Why a Temporary, 60-Day Lock on Devices Would Reduce Fraud | |
| b. | A Primer on Mobile Phone Hijacking, Bank Account Takeovers, and SIM Swapping |
| – Growth in Number of Mobile Identity Theft Incidents in the U.S. | |
| – Hijack Mobile Phones and Simultaneously Open Other Accounts of the Victim | |
| – Common Means of Obtaining Information Fraudsters Need to Hijack | |
| – FTC Recommendations for Mobile Carriers to Thwart Hijacking | |
| – Bank Account Takeover and Robbery via the Mobile Phone | |
| – Mobile Security Recommendations for Consumers | |
| – Consumer Steps to Protect Against SIM Swapping | |
| – Investigators Detail SIM Swapping of Cryptocurrency Account Takeovers | |
| – An Active Lawsuit Against AT&T for SIM-Swap Enabled Theft | |
| – Judge Throws Out the Damages Portion of Claim Against AT&T | |
| c. | "Moments Matter" in Blocking Identity Fraud: Why Number Porting Data is a Vital Tool in Stopping Account Takeovers |
| – Backgrounder on Number Portability in the US Market | |
| – Phone Numbers for Life & the Importance of Porting Data | |
| – Valuable Identity Intelligence to Access from the "Carrier of Record" | |
| – One Million Phone Ports a Day and the Account Takeover Threat | |
| – After SIM Swap: Fraudster can Capture Credentials in Several Minutes | |
| – PortData Validate's Value Proposition | |
| d. | Black Swan Solution Guide: Getting Porting History & Carrier Data to Verify Identity & Mitigate Account Takeovers |
| – Smartphone Identity Security: The Queen Guarding against Account Takeovers | |
| – PortData Validate: A New Risk Intelligence Service | |
| e. | PrologMobile: Save U.S. MNOs Hundreds of Millions a Year in Recovered Phones & Retained Customers |
| – Importance of the Used Mobile Device Supply Chain | |
| – The Long Life of a High Quality Smartphone | |
| – PrologMobile's History in the Mobile Phone Ecosystem | |
| – Cashing in Smartphones: The Conflict Between User & Carrier | |
| – A Plan for Returning More Used Phones to the Network that Sold Them | |
| – Proposal for More Efficient Reverse Supply Chain in Smartphones | |
| – Commercial Value of a Strong Reverse Supply Chain in Mobile Devices | |
| – Players and Relationships in the Smartphone Reverse Supply Chain | |
| – The Likely Impact of the Reverse Supply Chain in 5G | |
| – Conclusion | |
3. Behavioral, Network, and KYC Identity Analysis (34 pages)
 | |
| a. | LexisNexis Risk Solutions Takes Identity Checks from Physical/Biometric to Network-Behavior-Sharing with 7,000 Digital Businesses |
| – Sharing Anonymous Identity Intelligence Across Thousands of Businesses | |
| – ThreatMetrix Acquisition by LexisNexis | |
| – Backgrounder on LexisNexis Risk Solutions | |
| – The Evolution from Physical to Digital Identity Validation | |
| – Telecoms are Ready to Move from Physical to Digital | |
| – The Digital Identity Network Captures 7 Digital Parameters | |
| – The LexisNexis Global Digital Network Finds Fraudsters in Near Real-Time | |
| – Customer Privates Details are Not Shared in the Network | |
| – The Speed of Digital Entity Matching | |
| – System is Also Adept at Tracking Fraudsters Digitally | |
| – Catching Fraud at the Security Waterfall Saves Costs | |
| – How Consortium Identity Networks will Impact Telco Fraud Control | |
| – Getting Rid of the Need for Passwords | |
| – Top U.S. and European Banks are in the LexisNexis Consortium | |
| – Why Telecoms are Ready to Adopt a Digital Identity Network | |
| – How Biometrics Fits into the LexisNexis Network | |
| – Conclusion | |
| b. | NuData Analyzes Behaviors to Stop Automated Fraud Attacks & Identify Fake Customers Inside the Firewall |
| – Why Criminal Organizations Operate like an Infectious Virus | |
| – Telecoms Beginning to Adopt Identity Detections like Banks | |
| – NuData's Risk Solution Process: Engage, Identity, Decide | |
| – Hot Areas in On-Line Behavioral Protection | |
| – Where Fraudsters are Getting Better at Replicating Humans | |
| – The Complexity of Analyzing a Person's On-Line Habits | |
| – Probable Verification vs. a Certain Identity Match | |
| – Understanding the Identity Pain Point a Customer Wants to Solve | |
| – What Differentiates NuData's Behavioral Solution? | |
| – Telecom Acceptance of Behavioral Technology | |
| – Credit Bureaus and Network Identity Screening Technology | |
| – Conclusion | |
| c. | The Race to Develop Cross-Industry "Know Your Customer" Biometrics to Verify Identity Remotely |
| – Identity Verification in India | |
| – The Indian Government's UIDAI Identity Program | |
| – Know Your Customer and Verify Identity | |
| – Opportunities to Exploit the National Database | |
| – Facial Identification | |
| – Storing Facial Profiles Without Violating Privacy | |
| – Anti-Spoofing Measures for the Camera | |
| – Telecoms Must Buy Cross-Industry Solutions | |
| d. | NuData Shines Digital Behavior Light on Operating Telecoms Securely in a World Darkened by Identity Fraud |
| – Verifying via Multiple Factors of Interaction | |
| – Defining Digital Behavior | |
| – The NuData System of Digital Behavior Analysis | |
| – International Differences | |
| – US Market is Strong in eTail Protection | |
| – NuData Services Offered Through Mastercard | |
| – 50% Protection & 50% Optimization & Retention | |
4. Subscription Fraud & the Hub of Decision Intelligence (50 pages)
 | |
| a. | Mobileum Tackles Subscription Fraud and ID Spoofing with Machine Learning that is Explainable |
| – The Experts at Naming and Classifying Telecom Fraud | |
| – CFCA's 2019 Fraud Loss Estimate by Fraud Method | |
| – Grouping Subscription Fraud with Related Fraud Methods | |
| – The Threat Environment for ID and Subscription Fraud | |
| – Eight Threat Vectors for Subscription Fraud | |
| – Four Groups of Fraudsters Involved in Subscription & Identity Fraud | |
| – A Subscription Fraud System: An Automated Investigative Tool | |
| – Account Theft | |
| – Cash Flow Fraud by Dealers | |
| – Abnormal Contract Behavior | |
| – Credits Notes to a Customer Account | |
| – Mobileum's Subscription Fraud Approach using Machine Learning | |
| – The Importance of "Explainable" Machine Learning | |
| – Using Machine Learning to Solve Address and Naming Issues | |
| – Implementing a Subscription Fraud System at a Telco | |
| – Early Results of Engagement at a South African Operator | |
| – Conclusion | |
| b. | SAS Manages an Analytics Hub of Internal, 3rd Party, and AI Data for Telco Specific, Holistic Fraud Solutions |
| – Telecom Fraud Control Gains a Higher Profile | |
| – SAS Institute's Ramped Up Investment in the Telco Industry | |
| – The Two Primary Fraudster Threats & Persistent Legacy Frauds | |
| – Identity Analytics: the Precursor to Subscription Fraud Checks | |
| – The Hub that Ingests Data from Third Parties & the Telcos Themselves | |
| – SAS's Consultative Approach to Fraud Systems | |
| – Some Operators Have an Appetite for DIY Systems | |
| – Four Areas of Excellence Where SAS Provides Key Support | |
| – SAS Investments in Machine Learning/AI | |
| – Conclusion | |
| c. | Tackling Telecoms Subscription Fraud in a Digital World |
| – FICO's Cross-Industry Analytics & Fraud Fighting Business | |
| – Assessment of Telecoms in Subscription Fraud & Identity Verification | |
| – Improve ID verification via Selfie with “Liveness” Detection | |
| – Use Digital Identity Authentication to Reduce Friction | |
| – Use Machine-Reading to Verify Applications at Point of Sale | |
| – Do Real-Time Identity Analytics on the Credit Application | |
| – Better Align the Fraud and Credit Risk Teams | |
| – Build Up your Post-Book Fraud Analysis of Subscribers | |
| – Constantly Feed Case Intelligence Back to the Fraud Team | |
| – Build Intelligence into Your Subscription Fraud Models | |
| – Get Advice from Experts in Banking & ID Fraud Detection | |
| – How FICO Delivers Software & Consulting | |
| d. | Share, Educate & Tighten Controls: How to Instill a Strong Telecom Risk & Anti-Fraud Culture |
| – The Challenges of the African Market | |
| – Financial Infrastructure on the African Continent | |
| – Educating Consumers on Mobile Device Security | |
| – Educating Telcos about Fraud/Risk Education | |
| – The Revenue Assurance and Marketing Partnership | |
| – Risk Reward Awards Recognizes Achievers | |
| – Perspectives on the Value of Industry Forums | |
| e. | Telecoms Need to Step Up their Game in Subscription Fraud and Customer Onboarding Control |
| – Acquiring Customers at Low Cost & Minimum Risk | |
| – A Robust Onboarding Process for Mobile Subs | |
| – Mobile Phone Activity: a Great Risk Mitigating Tool | |
| – Demand for Money Laundering Controls | |
| – Steps in a Successful Customer Engagement | |
| – Fraud vs. Revenue Assurance Data Management | |
| – Solving Integration Complexity Issues | |
5. The Threat of Insider & Partner Fraud and Data Access Issues (26 pages)
 | |
| a. | Protecting Data from the Insider Threat: Veriato Closes the Security Gap with Massive Data Collection & Machine Learning |
| – Why Insider Threat Management Needs More Attention | |
| – On the Network vs. On the Endpoint | |
| – Why Machine Learning is Essential | |
| – Advice from the 2019 Insider Threat Maturity Report | |
| – Departments Who Need Access to Sensitive Monitoring Data | |
| – Coverage for Desktops and Android Cellphones | |
| b. | Verizon Insider Threat Report — Summary of Key Findings |
| – The Verizon Data Breach Investigations Report | |
| – Summary Research Findings | |
| – The Five Types of Insider Data Breach Threats | |
| – Scenario 1: Insider Agent Working on Behalf of Outside Entity | |
| – Scenario 2: 3rd Party Hardware — Embedded Data Collector in Firmware | |
| – The People and Asset Elements of the Insider Threat | |
| – The Importance of Coordination Among Stakeholders | |
| – Eleven Threat Countermeasures | |
| c. | Insider Fraud: How to Create an Anti-Fraud Culture in Your Telecom Organization |
| – Insider Fraud is a Massive Telecom Problem | |
| – Is There a Fraud Culture at Your Company? | |
| – Different Country Attitudes Toward Fraud | |
| – Insider Fraud Happens at All Department Levels | |
| – Screening the People Responsible for Fighting Fraud | |
| – Procedures to Put in Place to Fight Fraud | |
| – Preparation Around the Evidence to be Collected | |
| – Senior Management's Role | |
| – Consistency in the Anti-Fraud Program | |
| d. | A Candid & Anonymous Report from a Fraud Investigator |
| – Very Different Skills Required to Detect Insider Fraud | |
| – Example of an Insider Fraud Case with Many Manual & Tedious Processes | |
| – Can Big Data Really Help Me Investigate? | |
| e. | TELUS Analytics Users Get Productivity Boost from Internal Team of Data Access & Showcasing Experts-for-Hire |
| – Mission of the Telus Telemetry Team | |
| – What Telemetry Does to Benefit Internal Users | |
| – Why Telus Chose the WeDo RAID Platform | |
| – Engaging with Various Departments at Telus | |
| – Driving Predictive Analytics Campaigns for Users | |
| – The Evangelical Role of Telemetry's CMO | |
| – Telemetry's Growth Plans | |
6. High Tech Threats in Signaling & Mobile Malware (37 pages)
 | |
| a. | In the Era of Telecom Security Breaches, Mobileum Brings Signaling's Deep Detection Capability to the Fraud Fight |
| – The Merger of Mobileum and WeDo Technologies | |
| – Trusted Relationships Still Key to Signaling Security | |
| – Assessment of the Signaling Threat | |
| – How Telecoms can Respond to the New Threats | |
| – Signaling Improves Upon the Capabilities of CDR-Based Fraud Control | |
| – How Signaling aids International Revenue Share Fraud (IRSF) | |
| – Signaling's Role in Wangiri Fraud | |
| – Signaling and Data Fraud via Roaming | |
| – Signaling Aids SMS Bypass Detection | |
| – Signaling and Account Takeover via SMS Hijack | |
| – Dealing with a Multi-Protocol Telecom World | |
| – Network Equipment Providers' Role in Reconciling Multi-Signaling | |
| b. | Positive's Research Keeps Telecoms One Step Ahead of Signaling Hackers and Fraud Disasters |
| – The Invisible Pandemic in Telecom: Criminal Hackers & Fraudsters | |
| – Catalysts for Increasing Signaling Vulnerability | |
| – The Importance of Pinpointing Configuration Issues | |
| – Positive Technologies' Mission: White Hat Hacking & Security Research | |
| – Methods Positive Technologies Uses to Test Operator Networks | |
| – The IMSI — The Key Path to How Hackers Break into Mobile Networks | |
| – Breaking into a Mobile User's Bank Account | |
| – GSMA's Three Categories for Security Classifying Network Messages | |
| – Bypassing Signaling Detection | |
| – Positive's Signaling Security Firewall | |
| – The Challenge of Protecting Security in 5G | |
| – The Impact of Virtual Networks like NFV | |
| – The Internet of Things Security Vulnerability | |
| – Conclusion | |
| c. | Allot's Mobile Security: Network-based Protection that 21 Million Consumers & SMBs Subscribe to for One Euro a Month |
| – The Business of Deep Packet Inspection & Security | |
| – The Underserved Market for Mass Market Mobile Security | |
| – The Consumer is Confused about Mobile Malware Protection | |
| – No User-Side Intervention is Required | |
| – Commercial Successes in Mobile Malware at Vodafone and Telefonica | |
| – The Development of Allot's Malware Product | |
| – Guaranteeing the Customer's Protection Even when Off-Net | |
| – Commitment to the Customer Whatever Network They Use | |
| – Deep Telecom Security Knowledge Gives Allot an Edge over Security Giants | |
| – Conclusion | |
7. IoT & 5G Security and Connectivity (51 pages)
 | |
| a. | How Thales Embeds Comms Security for Electronic OEMs & Telecoms Delivering Next Generation IoT Systems & Services |
| – The Promise of Powerful, Highly Secure Embedded IoT Modules | |
| – The Thales Analytic and IoT Systems Business | |
| – Secure Modem Technology Built for OEM Manufacturers' Product | |
| – Use Cases Where Secure Modem Chipsets are Crucial | |
| – The Carrier Interface with the IoT Specialist Firm or Factory | |
| – Mitigating Fraud, Especially in a Roaming Scenario | |
| – The Future of Embedded Modems in the Automotive IoT Market | |
| – Conclusion | |
| b. | Subex Exploits its Deep Research of Global IoT Threats to Win Telecom, Industrial, and Automotive OEM Clients |
| – Subex's Positioning in IoT Security Monitoring & Protection Services | |
| – A Global Network of IoT Honeypots: Very Different Challenge versus IT Security | |
| – Collect Malware Data and Researching to Learn Their Signatures | |
| – Sorting Familiar Threats from New, Clever, and Purpose Driven Malware | |
| – Subex's IoT Activity with Telcos and Auto Industry | |
| – Digital Fraud Prevention: Subex's Signaling Approach | |
| – Conclusion | |
| c. | Positive Technologies: White Hat Hacking & Testing are Key to Signaling Security in the Era of 5G and IoT |
| – Parallels between Signaling and MS Window Security | |
| – Comparing the Security Issues of SS7, Diameter and GTP | |
| – A Deeper Dive into GTP Protocol Security Issues | |
| – How Hackers Exploit Signaling to Enable ID Theft and Account Takeovers | |
| – The Impact of Signaling Security on IoT's Future | |
| – The Special Challenges of 5G and Signaling Security | |
| – Will Telco's Drive to Win in 5G Compromise their Security? | |
| – Conclusion | |
| d. | Syniverse's Secure Global Access: Finally, a Neutral Third Party Service to Manage IoT Devices and Use Cases |
| – Why Digital Giants Have Delayed IoT Investment | |
| – The GRX Private IPX Network | |
| – High Security for the Largest IPX in the World | |
| – Daily Petabyte Consumption on the IPX | |
| – A Big Efficiency Play for Global Wireless Net | |
| – Secure Global Access for IoT | |
| – Supporting 50,000 Unique Non-Human Devices | |
| – Monitoring the Non-Human Use Cases in IoT | |
| – RCS Multimedia to Replace A2P Messaging | |
| e. | Senet's Cloud & Shared Gateways Drive its LoRaWAN Business |
| – LoRaWAN: An Alternative to Cellular IoT Connectivity | |
| – The Niche that Low Powered Wide Area Networks Occupy | |
| – The Origins of LoRaWAN and its Advantages | |
| – LoRaWAN Different Approach to Security: Control by Manufacturers | |
| – Deployment of LoRaWAN Gateways on Towers & Buildings | |
| – Senet's LoRaWAN Business: Regional to National Networks | |
| – Seven Key Uses Cases plus Prices and Capacities | |
| – Financial Flexibility & Incentives Attracts Cable Operators | |
| – LPWAN Virtual Networks: The Sharing of Gateways | |
| – Can LoRaWAN Have a Role in Home Security? | |
| – Conclusion | |
| f. | WeDo Explores the IoT Ecosystem in Search of Tomorrow's Pivotal Fraud & Business Assurance Solutions |
| – The New Product Development Challenge | |
| – When Telcos Don't Control the Data of IoT Devices | |
| – The Challenge of Acquiring Domain Knowledge | |
| – Fraud and Revenue Assurance Challenges in IoT | |
| – Many Different Slices of IoT QoS in a Connected Car | |
| – The Importance of Edge Computing in IoT Use Cases | |
8. Telecoms Monetizing Identity — Enterprise Partnering & Mobile Money (27 pages)
 | |
| a. | Subex's IDcentral Monetizes Telco & Enterprise Data to Deliver Digital ID & Risk Metric Services for Financing, KYC & More |
| – The Wealth Stored in Digital Consumer Intelligence | |
| – The IDcentral Service: Packaging Up Identity Info for Consumption | |
| – Using Telco & Enterprise Verifications to Solve Business Problems | |
| – Regions of the World where Telco Digital Intelligence is in Demand | |
| – Serving Micro Financing with IDcentral | |
| – Telcos are Increasingly Open to Monetize their Intelligence | |
| – Factors that Held the Market Back in the Past | |
| – Using IDcentral in an Onboarding & KYC Capacity | |
| b. | LATRO's Tips for Launching a Successful Revenue & Fraud Assurance Program for Mobile Money Operations in Developing Countries |
| – Mobile Money: A Key Money Maker for Telcos in the Developing World | |
| – Revenue Assuring Mobile Money is in High Demand | |
| – The Origins of Mobile Money | |
| – The M-PESA Success Story | |
| – The Main Actors in a Mobile Money Ecosystem | |
| – Mobile Money Transactions | |
| – The Risk Capabilities Necessary in Mobile Money | |
| – Checks and Balances Needed for Mobile Money RA | |
| – Fraud Controls for Mobile Money | |
| – Main Steps in LATRO's Implementation | |
| – Conclusion | |
| c. | Share, Educate & Tighten Controls: How to Instill a Strong Telecom Risk & Anti-Fraud Culture |
| – The Challenges of the African Market | |
| – Financial Infrastructure on the African Continent | |
| – Educating Consumers on Mobile Device Security | |
| – Educating Telcos about Fraud/Risk Education | |
| – The Revenue Assurance and Marketing Partnership | |
| – Risk Reward Awards Recognizes Achievers | |
| – Perspectives on the Value of Industry Forums | |
9. Number Databases & Wangiri Fraud (27 pages)
 | |
| a. | Wangiri Warriors: A Webinar on Solutions & Strategies for Fighting Call Back Fraud |
| – Wangiri: The Call Back Fraud | |
| – Contents of the On-Demand Webinar on Wangiri | |
| b. | Black Swan Solution Guide: The Value of an Authoritative Database of Global Telephone Numbers in Fraud Control |
| – A Solution Guide on Cloud Database of Global Telephone Numbers | |
| – Highlights of this Solution Guide | |
| c. | Lanck Telecom Raises Fraud Alarm for International Brands, Enterprise Call Centers & Carriers: Beware of Wangiri 2.0 |
| – International Wholesalers and Fraud Control | |
| – Lanck Telecom's Business | |
| – Wangiri 2.0: Call Back Fraud via a Website Form | |
| – Web Forms and Captcha Screen | |
| – Lanck's Fraud Management System | |
| d. | Black Swan Solution Guide: The IPRN Database |
| e. | The Early Warning Power of IPRN Test Call Detection in Blocking IRSF Fraud |
| – How IPRN Data Sets Up a Fraud Attack | |
| – The Flow of Criminal Operations in IRSF | |
| – IPRN Providers & Their Rate Cards | |
| – An Early Warning Database for IPRN Numbers | |
| – Customers Finding the IPRN Database Useful | |
| – Accessing the PRISM Database | |
| f. | Art of the Fugue: Bringing the Baroque World of Telecom Reference Data to Fraud Management |
| – Marrying Digital Tech with "Baroque" Tech | |
| – History of Biaas in Telecom Reference Data | |
| – A New Database Specific to IRSF Fraud Protection | |
| – Tracking Unallocated Numbers | |
| – Accurate List of Higher Tariff Destination Number Ranges | |
| – Pricing for the Fraud Number Database | |
| – Working with Fraud Control Solution Vendors | |
10. Real-Time Enterprise & Inter-Carrier Security Handshakes (24 pages)
 | |
| a. | Black Swan Solution Guide: SHAKEN / STIR Calling Number Verification & Fraud Alerting |
| – Building the Future of Business Telephony Trust | |
| – Contents of the SHAKEN/STIR Guide | |
| b. | Convenient & Spam-Free: Why 800-Number Texting (8MS) is a Growing B2C Channel in North America |
| – iconectiv and the Value of Telecom Connective Systems | |
| – The History of Text-Enabling Phone Numbers | |
| – Three Forms of Text-Enabling Toll-Free Numbers | |
| – Why Texting is Catching on as a Way to Contact Businesses | |
| – How Businesses are Taking Advantage of 8MS in North America | |
| – Consumer Expectations Change as More Companies Use 8MS | |
| – How an Enterprise Manages In-Coming Messages | |
| – The Future Outlook for B2C Texting | |
| c. | A&B Handshake: A Simple Way to Control Voice Fraud via an Out-of-Band Connection between A & B Operators |
| – Telecom Industry Handshakes | |
| – A&B Handshake: A Technical Solution to an Industry Headache | |
| – Annual Fraud Losses A&B Handshake Addresses | |
| – How the A&B Handshake Works: an On-Line Chat Analogy | |
| – Basic Requirements for Delivering a Voice Fraud Handshake System | |
| – Deployment of the Handshake Solution | |
| – Managing the Central Repository of Participants | |
| – Gaining Cooperation from the Broad Ecosystem of Comms Providers | |
| – Working Handshake & Integration is Already Achieved | |
| – Status of Deployment and Lanck Telecom's Business Model | |
| – The User Interface for Screening Traffic for Fraud | |
| – Securing the Information Exchanged via the Handshake | |
| – Operators Have Full Controlling of Their Blocking Process | |
| – Who Will be the Early Adopters? | |
| d. | White Paper: A Real-Time Cloud Service to Protect the Enterprise PBX from IRSF Fraud |
| – Protecting the Enterprise PBX through a Cloud Service | |
| – The Paper is Aimed at Enterprise and Telecom Fraud Managers | |
11. Perspectives on the Business of Telecom Risk (23 pages)
 | |
| a. | Opportunities & Obstacles: Consultant Luke Taylor Muses on the State of the Telecom Risk Assurance Business |
| – The Darwinian Struggle in the Telecom Risk Business | |
| – AI / Machine Learning vs. Human Analysis | |
| – Generic Platforms vs. Solving Customers' Key Issues | |
| – Why Telecom Needs Chief Data Officers | |
| – The Power of a Modular Assurance & Analytics Platform | |
| – Mobileum's Acquisition of SIGOS | |
| – Innovation in the RA/FM Market | |
| b. | Subex's COO: Machine Learning, Disruption and Adaptive Biz Models to Impact Telecoms in 2020 |
| – How can a Business Team Plot its Future Success? | |
| – Five Key Telecom Business Trends | |
| c. | A WeDo Conference Talk: Consulting & Analytics: Improving your Business Today, Enhancing it Tomorrow |
| – Conference Introduction | |
| – The Risk Challenges in Telecom Today | |
| – WeDo's Consulting Framework | |
| – Optimizing the Collections Process | |
| – Fraud & RA Problems at a Caribbean Operator | |
| – In-Store Mobile Handset Subscription Fraud Control | |
| – WeDo's WAVE: Professional Services & Tool Deployment | |
12. Strategies, Solutions & Market Analysis (67 pages)
 | |
| a. | Research Objectives & Methodology |
| – Research Methodology | |
| – A Focus on the Fraud Methods Side of Fraud Control | |
| – CFCA's 2019 Fraud Loss Estimate by Fraud Method | |
| b. | Market Analysis & Vendor Positioning |
| – The Heritage & Future Direction of Solution Vendors | |
| c. | Mobile Threats in Device Theft, SIM Swapping & Account Takeover |
| – Telecoms are now Crucial Security Watchdogs of the Digital World | |
| – Where the Greatest Fraud Risk Lies in Telecom | |
| – Fraud is a Wind that Always Blows | |
| – The Bank & Telcos Partnering to Stop Financial Account Takeovers | |
| – Verizon's Analysis of the Identity and Mobile Device Theft Problem | |
| d. | Network, Behavioral & KYC Identity Verification |
| – Identity Verification: The Last Firewall to Stop Fraud | |
| – Sharing Identity Intelligence across a Network of Thousands of On-Line Businesses | |
| – How the LexisNexis Digital Identity Network Tracks Digital Entities | |
| – Advantages and Assessment of Network-based ID Verification | |
| – NuData Analyzes Behaviors to Stop Automated Fraud Attacks | |
| – The Crisis in On-Line Automated Attacks by Fraudsters | |
| – What Differentiates NuData's Behavioral Solution? | |
| – NuData's Flexible Way of Delivering its Identity Verification Service | |
| – Market Positioning of KYC and Identity Verification Players | |
| e. | Subscription Fraud & the Hub of Identity Decision Intelligence |
| – Major Subscription Fraud Threat Vectors & Criminal Groups | |
| – A Subscription Fraud System as Automated Investigative Tool | |
| – The Importance of "Explainable" Machine Learning | |
| – How Mobileum Implements its Subscription Fraud System | |
| – SAS Institute Enters the Telecom Identity & Subscription Fraud Market | |
| – Identity Analytics: the Precursor to Subscription Fraud Checks | |
| – The Hub that Ingests Data from Third Parties & the Telcos | |
| – SAS's Consultative Approach to Fraud Systems | |
| – FICO Bridges the KYC and Subscription Fraud Gap | |
| – FICO's Nine Key Recommendations in Subscription Fraud and KYC | |
| – How FICO Implements its Solutions and Consulting | |
| – Market Positioning of Subscription Fraud Players | |
| f. | Insider/Partner Fraud & Data Access Issues |
| – The Verizon Assessment of the Data Breach Threat | |
| – Visual Recording of Device Screens to Discover Insider Threats | |
| – A Candid & Anonymous Conversation with a Fraud Investigator | |
| – Will Telcos Provide Data Lakes for Company-Wide AI Features? | |
| – A Dedicated TELUS Team Helps Analytic Users Find and Use Warehouse Data | |
| g. | High Tech Security Threats in Signaling & Mobile Malware |
| – Security Compromises: The Second Leading Fraud Method | |
| – Sizing up the Threat to Signaling | |
| – A Famous Case Where Signaling was Key to a Bank Takeover | |
| – The IMSI — The Key Path to Breaking into Mobile Networks | |
| – The White Hat Role of Signaling Security Specialty Firms | |
| – Exploiting Signaling Knowledge to Stop Fraud Voice, SMS & Data Fraud | |
| – Allot Addresses the Underserved Market for Mass Market Mobile Security | |
| – Market Positioning of Signaling Protection & Mobile Malware Players | |
| h. | IoT & 5G Security and Connectivity |
| – Thales Delivers Highly Secure Embedded IoT Modules for OEMs | |
| – The Internet of Things�rdquo;Its Security Vulnerabilities | |
| – A High Complex 5G Infrastructure will Enable IoT Services | |
| – A Global Network of IoT Honeypots Protects Enterprises | |
| – Subex's IoT Activity with Telcos and Auto Industry | |
| – Syniverse's Secure Global Access: a Neutral IoT Intelligence Service | |
| – Secure Global Access for IoT | |
| – LoRaWAN: A Low Cost Alternative to Cellular IoT Connectivity | |
| – LoRaWAN's Approach to Security: Control by Device Manufacturers | |
| – LPWAN Virtual Networks: The Sharing of Gateways | |
| – Market Positioning in the IoT and 5G Security Market | |
| i. | Telecoms Monetizing Identity — Enterprise Partnering & Mobile Money |
| – Digital Giants Battle for the Next Generation of E-Commerce | |
| – Where Telecoms are Delivering Value in Identity Monetization | |
| – Mobile Money: A Key Money Maker for Telcos in the Developing World | |
| – Monetizing Telco Data in Identity & Risk Services in Developing Countries | |
| – IDcentral: a Special Opportunity for Telco Monetization | |
| – Using IDcentral in an Onboarding & KYC | |
| – Voice Traffic Pumping Fraud Enabling Schemes | |
| – An Authoritative Database of Global Telephone Numbers to Fight IRSF & Wangiri | |
| – The IPRN Database and its Use in IRSF & Wangiri Fraud Control | |
| – Wangiri 2.0: A New, On-Line Path to the Callback Fraud Threat | |
| – Wangiri Warriors: A Webinar on Solutions & Strategies for Fighting Call Back Fraud | |
| j. | Real-time Enterprise & Inter-Carrier Security Handshakes |
| – The Erosion of Trust in Voice & SMS Communications | |
| – SHAKEN/STIR: Rebuilding Trust in Calling Party Verification | |
| – Texting Restore B2C Communications Trust? | |
| – A&B Handshake: A Simple Way to Control Voice Fraud | |
| – A Real-Time Cloud Service to Protect the Enterprise PBX | |
Addendum: Black Swan Telecom Solution Guides & Webinar (103 pages)
 | |
| 1. Yates Consulting: The IPRN Database and its Use in IRSF & Wangiri Fraud Control | |
| 2. iconectiv: SHAKEN / STIR Calling Number Verification: Restoring Trust & Mitigating Fraud in Business Voice Calls via | |
| 3. Lanck Telecom: Voice Fraud Management as a Network Service: Real-Time & Machine Learning-Based Protection on Demand | |
| 4. iconectiv: Getting Accurate, Up-to-the-Minute Phone Number Porting History & Carrier-of-Record Data to Verify Identity & Mitigate Account Takeovers | |
| 5. Oculeus: A Real-Time Cloud Service to Protect the Enterprise PBX from IRSF Fraud | |
| 6. iconectiv: The Value of an Authoritative Cloud Database of Global Telephone Numbers in Fraud Blocking & Business Analytics | |
| 7. Arraxe: Expanding the Scope of Revenue Assurance Beyond Switch-to-Bill's Vision | |
| 8. Webinar-on-Demand: Wangiri Warriors — Solutions & Strategies (55-minute MP4) | |
Expert Contributors
TRI conducted in-depth interviews with dozens of experts for this report. Here are bios of some of the key people who contributed their perspective:
Arnd Baranowski founded Oculeus in 2004 and has been the sole managing director ever since. With his background in aerospace technology, Arnd brings over 20 years of experience in software engineering and development of innovative solutions.
Under the premise that every problem has a solution, Arnd and his team continue to develop effective system solutions for managing telecommunications and quickly responding to the ever-changing needs of the global market.
Robert is Vice President of Marketplace Innovation at NuData Security. He is an industry-recognized technologist, thought leader, and advisor with over twenty-five years of experience in retail, payments, financial services, and cybercrime investigation and prosecution.
Robert brings his industry insight and vision to drive market-leading products and services for NuData Security, and is the public spokesperson for the organization. He is passionate about bringing safety to the digital world in the shape of cutting-edge technologies, so companies and end users don’t have to worry about risks from cybercrime.
In previous roles, Robert served as the Global Head of Payments, Security and Fraud for StubHub, as the Head of Consumer Security for Wachovia and Golden West Financial, and continues to advise early stage startups.
Carla Cardoso is the Head of WeDo Analytics Center at WeDo Technologies. She is an advanced analytics manager with over 20 years of experience in BI and Advanced Analytics projects.
Her degrees in both Statistics and Management make the perfect mix to respond to day-to-day challenges in different business areas, such as Banking, Telco, Retail, etc. and in different business objectives like Discount Analytics, Sales Forecast or Fraud Prediction.
Miguel Carrero is the SVP & General Manager of the Security Business Unit of Mobileum. In this role, he is responsible for the strategy and execution of all aspects of the Security business of Mobileum as well as its financial performance.
Mr. Carrero has over 20 years of executive experience in companies at different stages (from early stage start up to large multinational corporations) in the telecommunications and cybersecurity fields.
Miguel joined HP Spain in 1998 and then was relocated to the headquarters in Palo Alto (USA) where he held a variety of executive positions within the Telecommunications and Service Providers industry vertical, ultimately serving as general manager of a business unit within.
Miguel pivoted to Cybersecurity in 2013 as he moved to be the Head of Products and Solutions for ArcSight (Enterprise Security Products), where he held responsibility for the strategy, portfolio creation, evolution, go-to-market strategy and overall financial performance of the business.
At the end of 2016, he joined Siemplify a ventured capital early stage start-up in the Security Orchestration Automation and Response (SOAR) taking the company through 3 rounds of investment (USD 58M in total) and from zero to multi-million Annual Recurrent Revenue (ARR).
Mr. Carrero joined Mobileum in August 2019, while still serves in the Investors and Advisory board of Siemplify and the Advisory Board of FixNix, a SaaS start up in the Governance Risk and Compliance market.
Miguel holds a Master's degree in Economics from the Universidad Pontificia Comillas (ICADE), an Executive MBA from IESE and Telecom Strategy & Marketing Executive Program from INSEAD, Paris.
Bruce Chatterley is CEO and President of Senet. He is a seasoned business leader and entrepreneur, and brings more than 25 years of experience building successful high growth technology businesses.
Bruce most recently operated as an Independent Growth Consultant to global fiber optic telecommunications providers, based in London UK. Immediately prior, Chatterley served as CEO for Layered Technologies, a provider of secure cloud hosting services for Government, Financial Services and Healthcare applications.
He is also an experienced telecom leader, serving as CEO of cloud-based VOIP firms Broadvox and Speakeasy. In addition, he is a former senior executive at Ameritech and US West.
Bruce has also been an early leader in the development of the Software As A Service industry, having served as CEO of ViAir and President of eServices for Concur Technologies.
Earlier in his career, he also held Senior Sales and Marketing positions at GE and IBM. He earned his BSBA from Central Michigan University and his MBA from the Kogod College of Business Administration at American University.
Bruce currently serves as a Board member for London-based technology firm Snupps, Inc., Bigleaf Networks, and Clevest.
Chris Drake, Chief Technology Officer at iconectiv, is responsible for internal and external technology initiatives at iconectiv including emerging opportunities in mobile content, CyberSecurity, mobile identity, virtualization and M2M/IoT.
Drake began his career at Bell Northern Research and has over 25 years in the Telecommunications industry. Prior to iconectiv, Chris held executive positions at Aricent Group, Neustar, Sonus Networks, Telcordia Technologies, and Advanced Switching Communications. Drake also serves as an advisor to a number of technology startups and the Canadian Consulate Tech Accelerator @ NYC.
Drake is also on the board and executive committee of the Alliance for Telecommunications Industry Solutions (ATIS) and chair of the ATIS TOPS Council. Drake has served on the Industrial Advisory Board for the Security and Software Engineering Research Center (S2ERC IAB) through Georgetown University and the National Science Foundation.
Moshe Elias is Director of Product Marketing at Allot. He is responsible for marketing Allot's security solutions and security-as-a-service platforms to communication service providers and cloud providers that protect consumer and enterprise customers.
Moshe has more than 26 years of experience in security and information technology working with a range of customers from SMBs and enterprises and to governments and communication service providers and has a customer-centric approach to doing business.
Prior to his role at Allot, Moshe served as a solution expert for Check Point Software Technologies where he was responsible for developing the Check Point Software-Defined Protection (SDP) Data Center architecture for the Private and Public Cloud.
Moshe began his career in IT at Cisco Systems, serving in roles that spanned the IT and security spectrum from engineering and business development to sales and marketing over a 12-year period.
Mike Gilbert, Senior Account Director at iconectiv, is responsible for marketing, selling, managing, supporting and promoting TruReach Toll-Free 8MS. As a trusted business leader, Gilbert has diverse, progressive experience in telecom sales engineering, software development, project and program management and new business development.
Gilbert has spent his entire carrier in the Telecom sector, starting as a Software Engineer on Government Communications projects and moving on to integrate Voip Services Internationally.
Gilbert finally discovered his true expertise in the Toll Free industry where he now sits on 3 Industry standards boards. Gilbert holds a Bachelor of Science in Computer Science from University of Delaware.
John Haraburda, Principal Solutions Engineer Director at iconectiv, is responsible for managing critical business operations and spearheading business development to help customers solve real world problems.
John supports the iconectiv TruNumber Protect and Routing solutions which bring network and margin optimization to carriers around the world. By proactively addressing traffic in the carrier network, iconectiv enables our customers to mitigate risk for fraud; maximize their margins and efficiencies; and optimize the performance of existing staff and systems.
John has extensive experience in bringing revenue assurance and fraud solutions to the global market. Prior to iconectiv, John served in roles as Product Line Management and Solutions Engineering; Head of Revenue Assurance and Fraud; and management positions in billing, program management and finance.
Seth Heine is the CEO/Founder of PrologMobile. He is a serial entrepreneur with a knack for start ups in the electronics recycling and sustainability space. Mindful that our fragile little blue planet needs all the help it can get, Seth likes to be involved in anything that promotes common sense solutions that benefit people and the environment.
Guy Howie, CEO of Biaas, is a Charted Accountant (CPA in the US) and Certified Information Systems Auditor. Having read Chemistry at University, Guy started his career in Finance working for various companies including Ernst & Young in London.
Guy subsequently began his Telecoms career in 1999 within the Cable Industry (was known as The Cable Guy!), and after several years saving big bucks leading teams in Revenue Assurance and Business Intelligence, Guy found an opportunity to set up Biaas in 2006.
Guy has a family, loves to travel, and will be off windsurfing whenever the wind is blowing hard.
Jimmy Jones, Telecom Business Development Lead, Positive Technologies (https://positive-tech.com/)
Jimmy Jones is Telecom Business Development Lead at Positive Technologies. He has worked in telecoms for over twenty years, developing a wide range of expertise through a variety of engineering roles within major operators such as WorldCom (now Verizon), and vendors including Nortel, Genband and now Positive Technologies.
Jimmy began his career working extensively on legacy telecom exchanges, moving from maintenance, to commissioning and integration, and then specializing in protocol interoperability testing. In 2005, he transitioned into telecom security, taking up a position with a vendor specializing in SIP and Session Border Controller equipment.
Over the next 11 years, Jimmy was on the front lines as the customer base moved from Tier 3 and 4 wholesale carriers, to Tier 1 operators using SIP for peering and access, as part of the move to IMS and LTE networks. He joined Positive Technologies in 2017 to once again widen his horizons in information security, while utilizing his extensive experience of telecom operations.
Patrick Knight is the Senior Director of Cyber Strategy and Product Management at Veriato, an innovator in actionable user behavior analytics and a global leader in insider threat protection, where he helps organizations protect critical data from threats by trusted insiders.
For over 17 years, his cyber security career has helped enterprises protect against online threats through the development of anti-malware, network intrusion detection, computer and network forensics and encryption technologies.
He is a writer and speaker on topics of cyber security and privacy in multiple forums including NITSIG and Virus Bulletin. He is a 12-year veteran of the U.S. Intelligence Community and the United States Army in the fields of Signals Intelligence and Cryptanalysis and a Russian and Serbo-Croatian Linguist.
He can be reached on Twitter at @PatrickKnight70 and on LinkedIn at linkedin.com/in/PatrickKnight70
Jason Lane-Sellers is Director of Fraud & Identity at LexisNexis Risk Solutions, which provides an end-to-end platform for digital identity intelligence and trust decisioning.
He is a highly experienced fraud and revenue assurance professional who has been working in the Fraud & Risk areas of the telecom industry for over 25 years, with leading global operators.
Jason is also President and member of the Board of Directors of the CFCA (Communications Fraud Control Association), was previously the vice-chair of Fraud Intelligence subgroup of the GSMA Fraud Forum, and one of the team leaders of the Forum's Fraud Management Group.
Jason's expertise encompasses fraud and risk prevention strategy, operational effectiveness, fraud prevention technology and solutions and risk prevention best practice.
Bernardo Lucas was appointed Chief Marketing and Strategy Officer of WeDo Technologies in 2017.
Prior to joining WeDo Technologies, Bernardo worked as Project Leader at U.S. based Boston Consulting Group (BCG), where he led technology, media, telecommunications, retail and financial services consulting projects. He holds an MBA from INSEAD with distinction.
Rohit is responsible for delivering business growth using innovation and product strategy at Subex. He leverages his expertise in artificial intelligence (AI), analytics and digital services along with his experience in risk and fraud domains to build new offerings, drive business growth and deliver great customer experience.
Prior to this, Rohit was the Head of Subex’s Business and Solutions Consulting Group (BSCG) and has over 20 years of rich experience in delivering solutions and consulting to telecom operators across the world. He frequently represents Subex at industry forums.
Before joining Subex, Rohit worked with companies like Crompton Greaves and Kirloskar Electric Company. He is a graduate in electrical and electronics engineering from University of Mysore, India.
Joining WeDo Technologies in 2009, Carlos Marques previously held roles in marketing and sales for IT companies. Carlos is WeDo Technologies’ product marketing manager, the leader of the company product board - the “meeting point” for product & services strategy at WeDo Technologies. Carlos is also the person responsible for managing the product roadmap process in the company.
Carlos Martins is the Head Of Engineering at Mobileum Risk Business Unit. Joining the company in 2012 to build a UX strategy, Carlos has more than 16 years of experience in the development and architecture of rich internet applications and SaaS products.
Currently leveraging Mobileum's extended technology expertise, Carlos is leading the transformation project to evolve the company's product portfolio toward public, private, and edge cloud architectures while also exploiting the latest AI/ML enhancements towards full 5G support.
Sergey Okhrimenko is Chief Operating Officer at Lanck Telecom. He has been COO since 2014 and draws on his wide experience in the telecom industry.
He started at Lanck Telecom as Business Development manager in 2005, then moved to an Account manager in 2006. After rising to Head of the Analytical Department in 2008, he became the Revenue Assurance Manager in 2010.
Sergey graduated from the Leningrad Institute of Technology in 1991.
Shankar is the Founder and CEO of Fraud Risk and Security Research Labs (FRS Labs). A Certified Fraud Examiner, Shankar's experience range from business planning and analysis to development and deployment of complex intelligence systems. Over the past 18 years his work has included enterprise architecture, new product development and fraud prevention for Telecoms, Financial Institutions and Governments.
Shankar obtained his Engineering from PSG College of Technology, India and an MBA from University of Leicester, UK. Shankar is also a member of the Association of Certified Fraud Examiners and ACFE Bangalore Chapter.
Mel Prescott is a Principal Consultant in FICO's telecommunications practice, helping companies to use the most advanced analytics, decision rules, orchestration, mathematical optimisation and more.
He provides subject matter expertise, thought leadership and market understanding that translates industry needs into FICO solutions.
With 15+ years of experience working in analytical telecoms roles, Mel has held credit & fraud risk management positions at EE, Orange and Bank of America and also holds an MSc in Analytical Credit Risk Management.
Andy Procter is an experienced consultant within FICO Advisors. Andy joined FICO in 2011 but has worked in the fraud space since 2000. Andy brings experience in application fraud, transactional fraud, and credit risk, from a range of areas including financial services.
Andy has had roles from end-user to head of fraud, has worked in both client-side and supplier-side roles, and has detailed knowledge of rules software, analysis, performance management and fraud organisation. As a result, Andy has a broad understanding of our client's needs.
Don Reinhart is the Co-Founder and Chief Technical / Operating Officer of LATRO Services, Inc., providing technology leadership to the company's telecom managed services as well as software and hardware platform development.
Don has been involved with LATRO since its inception and has more than 20 years of experience working with leading telecom vendors and operators around the world.
Don has worked extensively on the design and implementation of network and fraud solutions within Asian, African, and Middle Eastern markets.
The specialty bypass fraud detection and control solutions provisioned by Don and his LATRO team routinely reverse losses and increase top line revenues of its clients.
In addition to telecom operators, he has worked with regulators to architect programs aimed at improving services within national markets.
Don holds a BS in Physics from Bucknell University and a MBA Finance degree from Johns Hopkins University. He was employed at Tektronix before joining the LATRO team.
Gary Richenaker, Principal Solutions Architect at iconectiv has been in Telecommunications for over 38 years. His role is to monitor and understand new technologies, to assess its impact on the existing products and services as well as identify how that technology can be used in the formulation of new products and services.
Prior to the iconectiv assignment, Gary served as Senior Director — Strategic Technical Initiatives at Neustar and prior to that as Chief Architect at Telcordia’s Interconnection Solutions. His career with iconectiv, Neustar, Telcordia, Bellcore, and Bell Laboratories has included responsibilities in technical analysis, strategic planning, marketing, planning and forecasting.
Gary has been involved in domestic and international standards since 1991 and presently holds a number of industry leadership positions including Board of Director of the SIP Forum, Co-Chair of the ATIS Test bed Landscape Team (TLT) and editor the ATIS/SIP Forum IP NNI Routing Document.
Gary has also been Rapporteur of the ITU-T Numbering Question (SG2/1), Chairman of the US ENUM Forum, and Chairman of the US Study Group A Ad-Hoc on Numbering, Routing and Services. He is also Past-Chairman of the US IMSI Oversight Council (IOC), and the US Study Group A Ad-Hoc on ENUM.
Gary holds an MBA and a BS in Economics.
Shankar is the Chief Operating Officer of Subex, responsible for Sales, Marketing, Engineering and Delivery. Shankar is a management professional with close to two and half decades of experience in Telecommunications, Cloud and PaaS.
He comes with extensive international experience and ability to scale businesses in highly competitive environments, particularly around the SaaS space.
Being an ex-Subexian, Shankar joined Subex from Plivo, a Y- combinator company where he held the position of Head of Growth. He holds a Management degree from IMDR Pune, with a specialization in Sales & Marketing with a minor in Systems.
He has an undergrad degree in Electronics Telecommunications Engineering and is a graduate in Triple Mathematics.
Igor Skutsenya, Fraud Management System project manager and RCS team leader at Lanck Telecom, combines 6 years' experience in the telecom industry, being a member of LANCK team since 2017.
He is involved in revenue assurance & anti-fraud projects, management and business development sectors, and presents LANCK Telecom global anti-fraud initiatives in GSMA, CFCA, GCCM and other mobile associations & events.
Stephen Spellicy is the VP of Strategy & Marketing, Analytics and IoT Systems Group at the Thales Group. He is a 20-year veteran in the Information Technology industry with domain expertise in enterprise software, networking, storage and virtualization technologies. He has held a host of senior and executive level positions in product management, marketing, business strategy and planning.
Most recently, Stephen led Hewlett Packard Enterprise's product management organization for the information management and governance business, delivering market-leading data protection, archiving, big data analytics and compliance software products to 40,000+ customers worldwide.
Stephen has also held senior leadership roles at EMC, Lucent Technologies, EqualLogic (Dell), Njini, Inc., and Virtensys, Ltd. Stephen holds a Bachelor of Arts from Berklee College in Boston, MA.
Thomas Steagall is the VP North America at Mobileum. He is a seasoned executive with 18+ years of experience in the Telecom Industry, providing consulting services globally to Tier 1 companies.
He specializes in Risk Management, Revenue Maximization, Asset Optimization and Operational Excellence. He has a very solid know-how on the entire IT/Cloud space -- OSS/BSS/Digital transformation journeys as well as on Business Process Management.
Luke is a seasoned business executive with a deep knowledge of telecoms fraud management and business assurance from his 20 years in the industry working for a risk management software vendor.
He founded Lateral Alliances in 2017 to offer business management and consultancy services focused in the IT sector and specifically telecoms risk management.
Luke has also established his own not-for-profit awards body, Risk Reward Awards with the goal of recognizing the best work done by risk professionals in the telecoms sector.
Sundeep Tengur is a fraud and financial crimes specialist within the Global Fraud and Security Intelligence Practice at SAS Institute. He provides guidance on industry best practice, educating prospects on various fraud modus operandi and designing end to end solutions to mitigate fraud risks.
He is a Certified Financial Crime Specialist (CFCS), certified in retail banking conduct of business (CertRBCB) and a Certified Anti-Money Laundering Specialist (CAMS) with many years of experience in devising fraud mitigation strategies in financial services and communications.
Kathy Timko, Head of the Local Number Portability Administration (LNPA) Services at iconectiv, is responsible for the U.S. Number Portability business for the company. In this position, she oversees all aspects of developing, transitioning, launching, and operating iconectiv's LNPA service as the number portability provider for the US Telecommunications industry.
Kathy has more than 25 years of experience in telecom and tech companies. She holds several Advisory Board roles, including Rutgers CX, and served as an Executive in Residence at Columbia University’s Technology Ventures group. In 2009, Timko was appointed Chief Operating Officer of Canoe Ventures, LLC, a joint venture of the six largest cable firms, and became interim CEO in 2011.
Before joining Canoe, she held several senior management positions at IDT Telecom, including COO and CTO. She was appointed to the IDT Telecom Board of Directors in 2001 and served as an independent director on the board of Motionbox from 2006 to 2010.
Timko holds a Bachelor of Science degree in Mechanical Engineering from Virginia Tech and a Master of Science degree in Computer Science from Boston University.
John Wick serves as Senior Vice President and General Manager, Service Provider Group, and is responsible for the management and growth of Syniverse's next-generation networking solutions. He also leads product development across this line of business, which includes Syniverse's Connected LTE, IPX, IMS, SS7 and Turnkey product lines.
John joined Syniverse in 1993 and was initially responsible for managing the network operations department. Over his tenure, he has held management positions in the operations, research and development, technology, business development, and product management groups.
Prior to joining Syniverse, John was a systems integrator with Verizon and, earlier, an electronic communications and switching systems technician for the U.S. Air Force.
He earned both bachelor's and master's degrees in business from Nova Southeastern University. He also holds an associate's degree in electronic engineering technology from the Community College of the Air Force, and he is a certified Six Sigma Black Belt.
Ryan Wilk was the Vice President of Customer Success for NuData Security, a Mastercard Company. Previously, he was the manager of Trust and Safety at StubHub and spent eight years with Universal Parks & Resorts in various eCommerce roles. NuData Security predicts and prevents online fraud, protecting businesses from brand damage and financial loss caused by fraudulent or malicious attacks. NuData Security analyzes and scores billions of users per year and services some of the largest eCommerce and web properties around the globe.
Colin started his working life in Law Enforcement in New Zealand, then after 18 years moved to a Risk and Fraud Management role in Telecom New Zealand.
After 12 years there, he moved to Vodafone New Zealand and for the next 12 years had roles with Vodafone in New Zealand, Australia, Germany and the UK, leaving Vodafone in 2012 as Group Head of Fraud Management and Investigations, having had responsibilities for managing fraud and investigations right across the Vodafone footprint.
Colin has held Management positions in the GSMA Fraud Forum, CFCA, FIINA and Pacific Partners.
He is currently managing his own firm, Yates Fraud Consulting Limited which consults back to industry operators to review their Fraud and Revenue risk maturity. He also manages an IPR Test Number database currently in use by some of the world's largest operator groups.
Colin is a Certified Fraud Examiner (CFE) and is also a Fraud Adviser to PITA (Pacific Islands Telecommunications Association).
Mark Yelland has been working in the revenue assurance and fraud space for over 20 years. For the last five, he has run a small consultancy firm, RAAIIM, targeting the smaller and newer operators, helping them get started or improve their revenue leakage and risk management. Showing them what can be achieved with minimal spend - getting more out of their existing systems, or developing tools using open-source products.
Like all engineers, he enjoys solving problems of all types, trying to find elegant, cost effective and simple solutions to big problems. His engineering training comes from the degree course at Cambridge University and his business skills come from the Open University MBA.
Kiran Zachariah is a leader in the field of IoT security. As the VP of IoT Business Solutions as Subex, Kiran is responsible for building and strengthening Subex's presence in IoT Security by driving revenue growth, setting and executing the strategic and technology direction of IoT Security business. He is building the current team to capitalize on Subex's investment in the IoT space.
Kiran has over 17 years of telecom experience in security, network analytics, and machine learning. Kiran also heads the Procurement and IT functions of Subex.
About TRI
Technology Research Institute (TRI) has been reporting and researching telecom software and systems markets since 1994. Our industry reports have covered the gamut of telecom systems from billing and service assurance... to customer care and provisioning.
In recent years, TRI’s research director and owner, Dan Baker, has authored major reports on Fraud Management, Business & Revenue Assurance, Telecom Wholesale Solutions, and Telecom Analytics/Big Data.
TRI’s Black Swan Telecom Journal is where we interview top experts in areas such as revenue protection, fraud control, security, business assurance, analytics, and optimization systems.
The Black Swan Series of Telecom Solution Guides are deep dive one-vendor-specific papers that focus on one Solution category in Risk and Assurance. These objectively written papers under TRI’s editorial and industry analyst guidance feature the commentary of solution vendor experts.




































